
DDoS attacks are one of the most common threats faced by websites and online services today, making it essential for organizations to prevent DDoS attacks before they impact availability. These attacks are designed to overwhelm systems with excessive requests, causing services to become slow, unstable, or completely unavailable. Because digital platforms depend on constant uptime, even a short disruption can lead to serious operational and business challenges.
The good news is that DDoS attacks are preventable. With the right strategies, tools, and planning, systems can be prepared to handle abnormal traffic and reduce the impact of attacks. This guide explains how to prevent DDoS attacks using clear, simple language so anyone can understand and apply the concepts.
What Is a DDoS Attack?
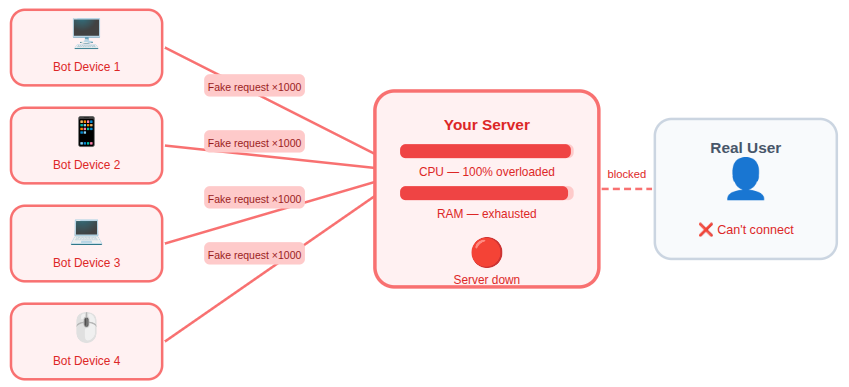
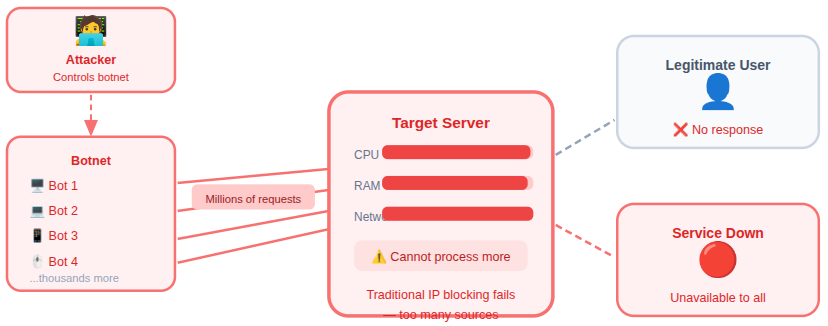
A Distributed Denial-of-Service (DDoS) attack occurs when a system receives more requests than it can process. These requests come from multiple sources, making it difficult to block them individually. The main goal of a DDoS attack is to exhaust system resources and prevent normal users from accessing services.
DDoS attacks do not focus on stealing information. Instead, they aim to disrupt availability and performance.
How DDoS Attacks Work
DDoS attacks work by sending repeated requests to a system until it cannot respond properly. Since the requests come from multiple sources, traditional blocking methods are often ineffective. The system becomes busy handling malicious traffic instead of serving legitimate requests.
Why DDoS Attacks Are a Serious Threat
DDoS attacks pose a major risk because they directly impact system availability and performance. Any online service that depends on consistent access can be disrupted when traffic suddenly exceeds handling capacity.
Key risks include:
- Service downtime: Systems become unavailable, preventing users from accessing services.
- Poor user experience: Slow loading and failures reduce user trust and satisfaction.
- Increased server load: Excessive requests strain system resources beyond safe limits.
- Loss of system reliability: Repeated attacks weaken overall platform stability.
- Long recovery times: Restoring services after an attack can take significant time and effort.
Because many services rely on constant connectivity, DDoS attacks can quickly escalate into major operational issues.
Types of DDoS Attacks
DDoS attacks occur in different forms, each targeting systems in a unique way. Understanding these types helps in choosing the most effective prevention techniques.
Volume-Based Attacks
These attacks overwhelm systems by sending extremely high amounts of traffic.
- They consume available bandwidth and prevent normal data flow.
Protocol-Based Attacks
These attacks target weaknesses in communication protocols.
- They exhaust system resources by misusing protocol-level functions.
Application-Layer Attacks
These attacks focus on specific application features.
- They are difficult to detect because they resemble legitimate user activity.
Identifying Early Signs of a DDoS Attack
Recognizing early warning signs helps reduce damage and response time. Small performance issues often signal the beginning of a larger attack.
Common warning signs include:
- Sudden traffic spikes: Unexpected increases in requests without normal patterns.
- Slow system response: Delays in processing legitimate requests.
- Frequent service timeouts: Systems fail to respond within expected timeframes.
- Unusual request patterns: Repeated or abnormal access behavior.
Monitoring these indicators allows faster action before systems become overwhelmed.
Key Strategies to Prevent DDoS Attacks
Preventing DDoS attacks requires a layered security approach that focuses on controlling traffic, strengthening server defenses, and preparing systems for abnormal load. By combining network-level controls, application protection, monitoring, and response planning, organizations can significantly reduce the risk of service disruption.
The following strategies explain the most effective ways to protect systems from DDoS attacks.
1. Network-Level DDoS Prevention
Network-level protection aims to stop malicious traffic before it reaches core systems. These controls act as the first line of defense.
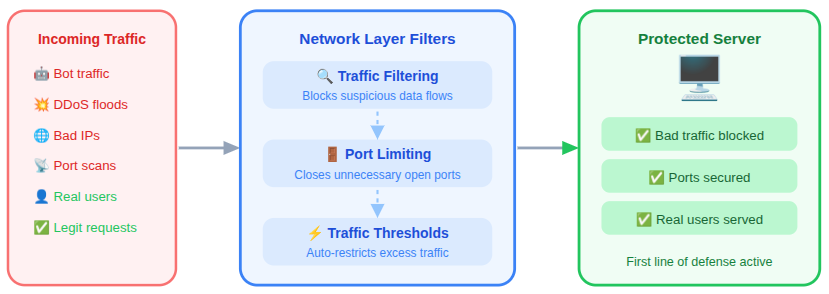
Effective practices include:
- Filtering unwanted traffic: Blocks suspicious or unnecessary data flows.
- Limiting unnecessary open ports: Reduces entry points for attack traffic.
- Using traffic thresholds: Automatically restricts traffic when limits are exceeded.
These measures help prevent excessive requests from reaching internal services.
2. Application-Level Protection
Application-level defenses focus on securing specific system functions and endpoints. These controls help identify and block harmful behavior early.
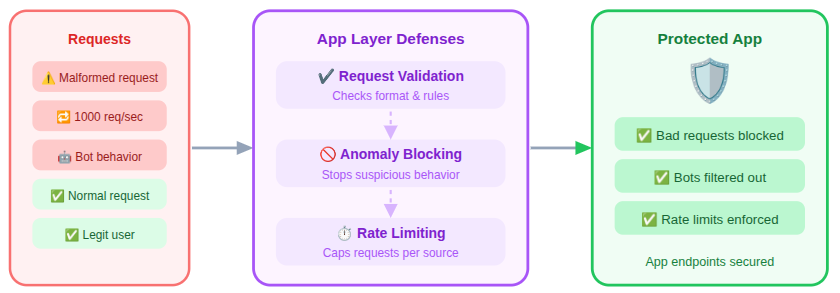
Important techniques include:
- Validating incoming requests: Ensures requests follow expected formats and rules.
- Blocking abnormal behavior: Stops repeated or suspicious actions.
- Limiting repeated actions: Prevents excessive requests from a single source.
These controls reduce the risk of targeted application-layer attacks.
3. Using Rate Limiting to Control Traffic
Rate limiting controls how frequently requests can be made within a defined period. This helps maintain system balance during high traffic situations.
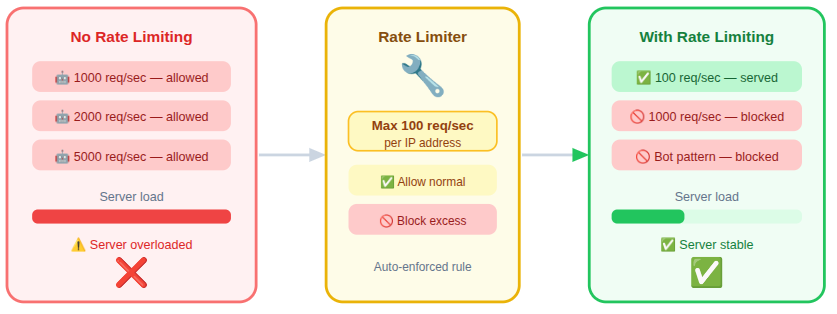
Benefits of rate limiting include:
- Preventing request flooding: Stops excessive requests from overwhelming systems.
- Reducing server overload: Preserves resources for legitimate users.
- Detecting automated traffic: Helps identify non-human request patterns.
Rate limiting is one of the simplest and most effective DDoS prevention methods.
4. Importance of Firewalls
Firewalls act as a control layer between systems and incoming traffic. They enforce rules that determine which requests are allowed or blocked.
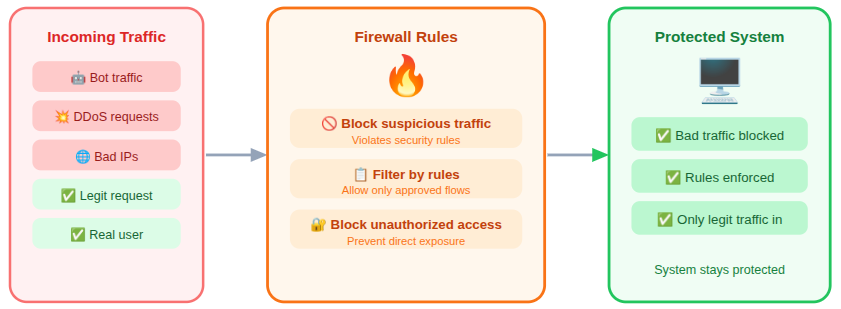
Firewalls help by:
- Blocking suspicious requests: Stops traffic that violates security rules.
- Filtering traffic based on rules: Allows only approved data flows.
- Preventing unauthorized access: Protects systems from direct exposure.
Web-focused firewalls are especially useful for defending against application-layer attacks.
5. Traffic Monitoring and Analysis
Monitoring tools provide visibility into traffic behavior and system activity. This visibility helps detect attacks early and respond efficiently.
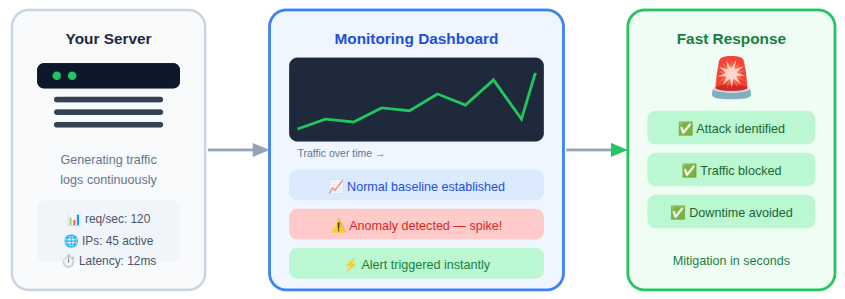
Key advantages include:
- Identifying traffic patterns: Establishes a baseline for normal activity.
- Detecting anomalies: Highlights unusual behavior quickly.
- Improving response time: Enables faster mitigation during attacks.
Consistent monitoring makes DDoS attacks easier to identify and manage.
6. Server Configuration and Hardening
Proper server configuration improves resistance against high traffic and malicious activity. Secure systems are harder to overwhelm.
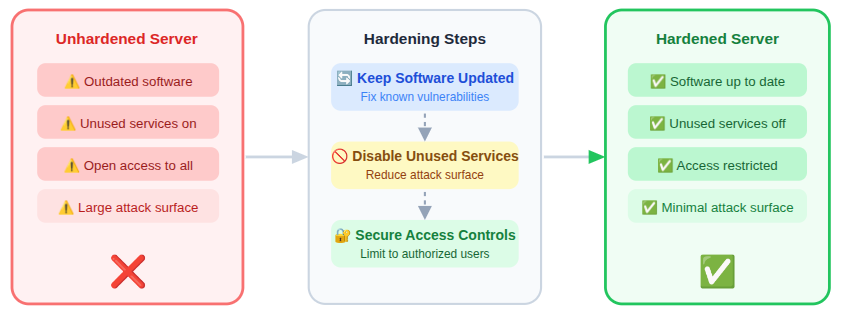
Server hardening steps include:
- Keeping software updated: Fixes known vulnerabilities.
- Disabling unused services: Reduces unnecessary attack surfaces.
- Applying secure access controls: Limits system access to authorized users.
These steps reduce attack surfaces and improve stability.
7. Load Distribution Techniques
Load distribution spreads incoming traffic across multiple resources. This prevents any single component from becoming overloaded.
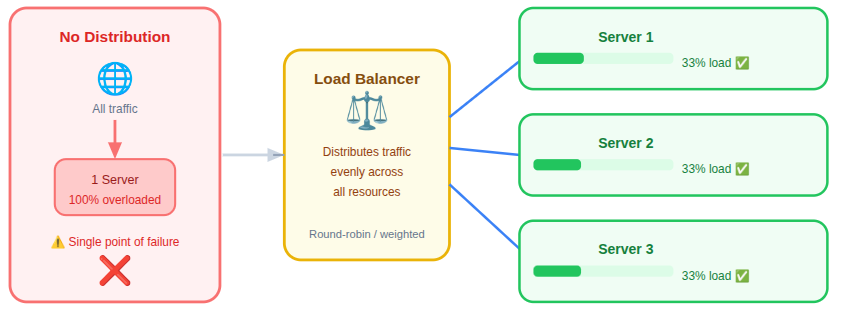
Advantages include:
- Improved performance: Balances workload efficiently.
- Better availability: Keeps services accessible during high demand.
- Increased fault tolerance: Reduces impact if one resource fails.
Load distribution helps systems remain responsive during high traffic events.
8. Incident Response Planning
An incident response plan prepares teams to act quickly during an attack. Clear procedures reduce confusion and downtime.
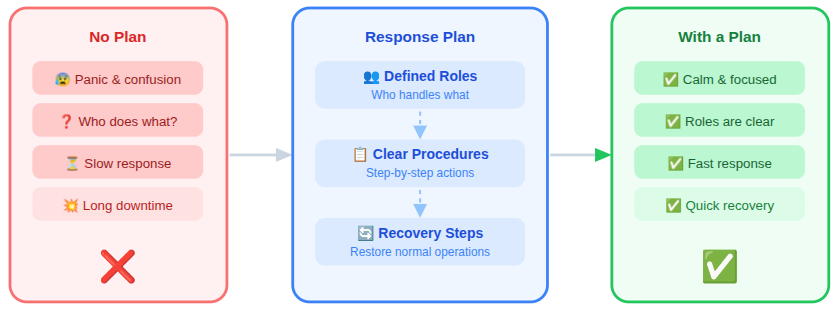
A strong plan includes:
- Defined roles: Ensures responsibilities are clearly assigned.
- Clear response procedures: Provides step-by-step actions to follow.
- Recovery steps: Outlines how to restore normal operations.
Prepared systems recover faster and experience less disruption.
9. Regular Security Maintenance
Security requires ongoing attention to remain effective. Regular checks help maintain strong defenses.
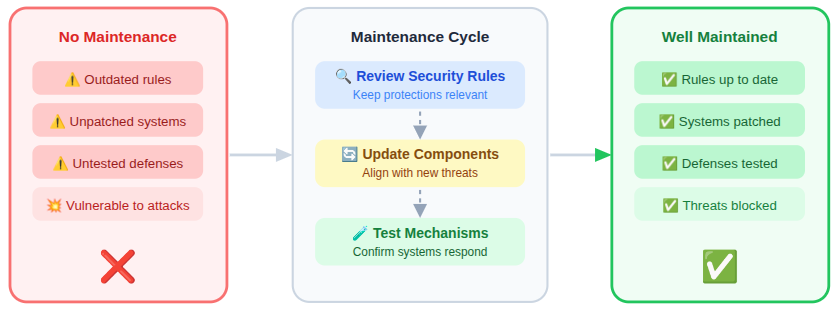
Regular maintenance should include:
- Reviewing security rules: Ensures protections remain relevant.
- Updating system components: Keeps defenses aligned with current threats.
- Testing protection mechanisms: Confirms systems respond as expected.
Consistent maintenance keeps defenses effective against evolving threats.

Building a Long-Term DDoS Defense Strategy
Long-term DDoS protection relies on multiple layers working together. A single solution is rarely sufficient.
A strong strategy combines:
- Network controls: Manages traffic at entry points.
- Application defenses: Protects specific system functions.
- Monitoring and planning: Enables early detection and faster response.
Multiple layers ensure better protection and long-term stability.
How ServerAvatar Helps Strengthen DDoS Protection
Modern DDoS prevention goes beyond simply blocking traffic. It requires continuous visibility, precise control, and proactive server management. This is where ServerAvatar helps strengthen server-level defenses and improve overall system resilience.
What is ServerAvatar?
ServerAvatar is a platform to simplify the hosting and management of servers and applications. It simplifies the process of deploying and managing PHP and Node.js based web applications on servers.
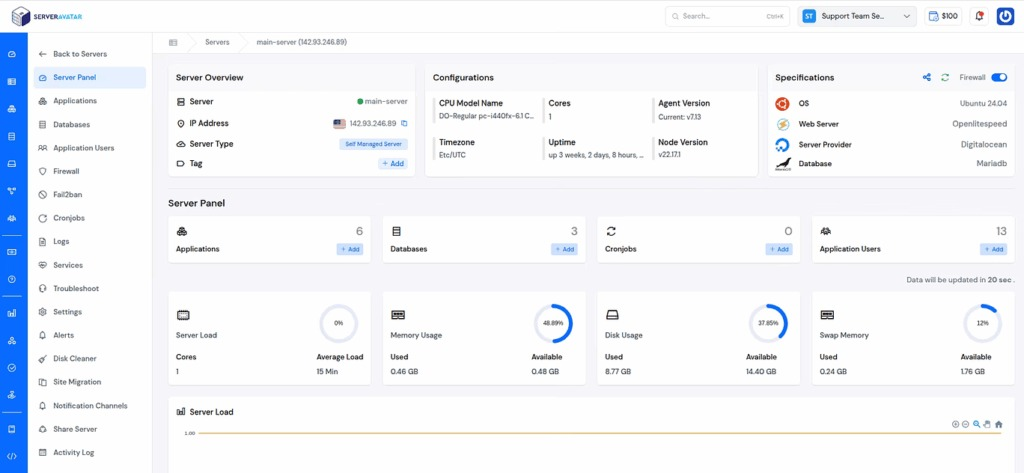
ServerAvatar provides a centralized server management platform designed to simplify security operations and maintain server stability during high-traffic situations. It enables administrators to monitor activity, optimize resources, and apply security best practices efficiently.
Key ServerAvatar Features That Support DDoS Prevention
- Real-time server monitoring
Tracks server activity and resource usage to help identify unusual traffic patterns that may signal early-stage DDoS attacks. - Detailed system insights
Provides clear visibility into CPU, memory, disk, server load, and process behavior, making it easier to detect abnormal load conditions. - Advanced security protection
Provides a unified security layer that includes firewall management, Fail2Ban protection, AI-bot blocker, and advanced rule sets such as 8G Firewall. Together, these features help block malicious traffic, prevent abuse, and reduce exposure to DDoS-related threats. - Service and process control
Enables users to manage running services and processes, ensuring system stability during unexpected traffic spikes.
By combining visibility, control, and simplified server management, ServerAvatar helps businesses build a strong foundation for long-term DDoS resilience while maintaining performance, uptime, and operational stability.
Strengthen Your DDoS Defense and Maintain Service Availability
DDoS protection is not a one-time setup but an ongoing process that requires the right mix of technology, monitoring, and preparation. By applying layered defenses, maintaining secure server configurations, and continuously reviewing traffic behavior, businesses can reduce the risk of service disruption and ensure long-term stability. Using a structured approach and reliable server management tools helps transform DDoS prevention from a reactive task into a proactive security strategy.
Conclusion
DDoS attacks remain a serious threat to websites and online services because they directly target availability and performance. However, with proper planning and the right preventive measures, their impact can be significantly reduced. Strategies such as network-level filtering, application-layer protection, rate limiting, traffic monitoring, server hardening, and incident response planning work best when implemented together. A layered defense approach ensures systems remain resilient even during high traffic or attack scenarios. By combining consistent security maintenance with proactive server management solutions like ServerAvatar, organizations can strengthen their DDoS defenses while maintaining performance, uptime, and user trust.
FAQs
1. What does the DDoS attack do?
The primary goal of a DDoS attack is to overwhelm a system with excessive traffic, making websites or services slow, unstable, or completely unavailable to legitimate users.
2. Can DDoS attacks be completely prevented?
While it may not be possible to eliminate DDoS attacks entirely, their impact can be greatly reduced through layered security measures, proper server configuration, and continuous traffic monitoring.
3. Why is a layered approach important for DDoS prevention?
A layered approach ensures that if one defense mechanism is bypassed, other controls are still in place. Combining network, application, and server-level protections provides stronger and more reliable defense.
4. How does traffic monitoring help prevent DDoS attacks?
Traffic monitoring helps establish normal usage patterns and quickly identify unusual behavior. Early detection allows faster response before systems become overwhelmed.
5. What role does server hardening play in DDoS protection?
Server hardening reduces unnecessary services and vulnerabilities, making systems more stable and resistant to high traffic loads during an attack.
6. How does ServerAvatar support DDoS prevention?
ServerAvatar simplifies server monitoring, security management, and resource control. Its features help detect abnormal traffic, manage services efficiently, and maintain server stability during traffic spikes.
